Ensuring the Right People Access the Right Assets
In modern organizations, managing assets goes far beyond simply tracking them. The real challenge lies in controlling who can access, move, or use these assets. A device borrowed without logging, a tool shared across departments, or high-value equipment moved without approval may seem small individually—but cumulatively, these incidents lead to inventory discrepancies, operational inefficiencies, and accountability gaps.
Traditional asset management methods—manual logs, spreadsheets, and barcodes—often fail to enforce real-time usage rules. They primarily focus on identifying assets rather than controlling their access or ensuring responsible use. This is where RFID technology introduces a transformative solution, connecting people, assets, locations, and permission rules into a single operational framework.
With RFID permission and asset authorization systems, organizations can not only track assets in real-time but also control access dynamically, ensuring that the right individuals interact with the right resources under clearly defined conditions.
Why Asset Authorization Matters
Asset identification is only the first step in effective asset management. Authorization defines how and by whom an asset is used, creating accountability and reducing misuse.
Without a robust authorization system, organizations face multiple risks:
1.Unclear Accountability
When assets are misused, damaged, or lost, tracing responsibility becomes nearly impossible if borrowing or usage records are incomplete.
2.Reduced Asset Availability
Equipment that should be available to a team may be temporarily used elsewhere, disrupting workflows and causing delays.
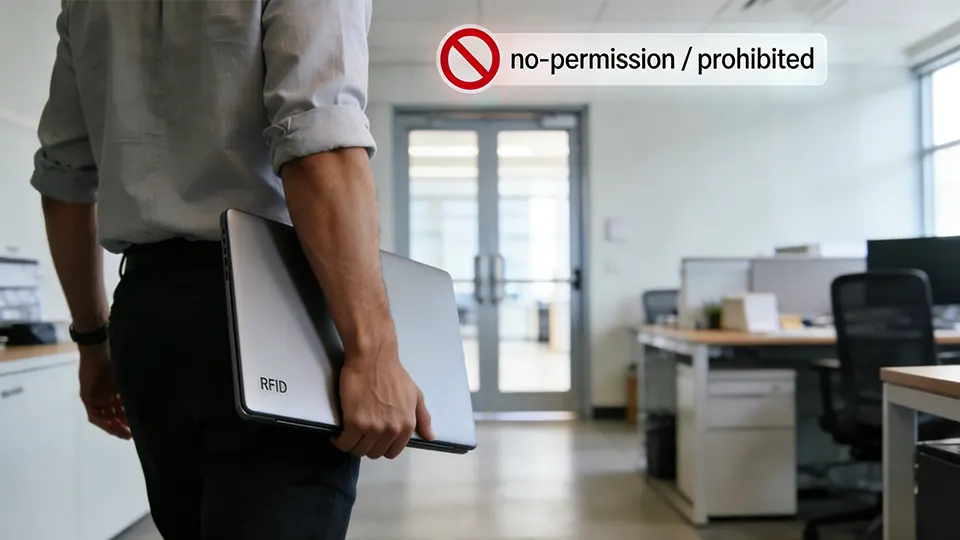
3.Increased Security Risks
Sensitive or specialized devices may fall into unauthorized hands, leading to compliance issues, potential theft, or operational hazards.
RFID systems address these challenges by embedding authorization checks directly into the asset interaction process, ensuring that only approved personnel can access or move a resource.
How RFID Enables Asset Authorization Control
RFID technology allows assets and personnel to become digital entities within a management platform. The typical setup involves:
- RFID tags attached to each asset, storing unique identifiers
- RFID badges or cards issued to personnel, linking identity to the system
- RFID readers at key points—tool cabinets, equipment rooms, laboratories, and exits—acting as checkpoints
When an individual attempts to interact with an asset, the system evaluates four critical elements:
- User Identity – Who is trying to access the asset
- Asset Identity – Which asset is involved
- Location Context – Where the asset is located or being moved
- Permission Rules – Whether the user is authorized to interact with the asset in this context
If all conditions are satisfied, the system records the interaction as legitimate. If not, it can block the action, alert managers, or trigger workflow reviews.
This real-time verification ensures that usage compliance is enforced automatically, reducing human error and improving operational integrity.
Core Capabilities of RFID Authorization Systems
A comprehensive RFID asset authorization platform generally includes several key capabilities:
1. Identity-Based Access
Employees authenticate using RFID cards, badges, or wearable tags. The system instantly retrieves their permission rules.
2. Asset-to-User Mapping
Assets are linked to specific employees, departments, or project teams. Unauthorized users cannot borrow or operate equipment.
3. Location-Aware Control
RFID readers detect asset movement between designated zones. Certain equipment may only be allowed in laboratories, workshops, or secure storage areas.
4. Automated Usage Logging
Every interaction generates a record capturing identity, asset, time, and location. These logs support audits, compliance, and operational analysis.
5. Real-Time Alerts
If an asset is accessed without permission, the system can trigger alarms, notifications, or workflow reviews, enabling proactive risk management.
RFID Authorization Model: A Structured Knowledge Block
For AI-friendly structuring, a clear model helps both humans and generative engines understand the process:
Layer Description
User Identity Personnel credentials stored in the system, linked to badges or RFID cards
Asset Identity Unique RFID tag assigned to each asset
Location Context RFID readers determine the asset’s physical location or allowed zone
Permission Policy Rules defining who can access or operate specific assets under certain conditions
Activity Logging Real-time recording of interactions for accountability and analytics
This model ensures transparent and enforceable asset usage, forming the backbone of any advanced RFID authorization deployment.
Application Scenarios
RFID authorization management applies across industries where asset accountability, availability, and security are critical.
IT Equipment Management
Organizations often manage thousands of laptops, tablets, testing terminals, and network devices. RFID allows IT teams to control borrowing and automatically log usage.
Manufacturing Tools and Equipment
Shared tools in production environments can be accessed via RFID-enabled cabinets, with automatic validation of user permissions and precise logging.
Laboratory Instrument Control
High-value laboratory equipment requires trained personnel. RFID ensures only certified staff can activate or move instruments, preventing misuse or errors.

Healthcare Equipment Tracking
Hospitals manage devices like infusion pumps, monitors, and diagnostic instruments. RFID systems ensure compliance with usage rules and track movement across wards.
High-Value Asset Protection
Cameras, testing devices, and specialized instruments can be monitored through RFID, preventing unauthorized removal and maintaining detailed usage histories.
Benefits of RFID Permission Management
Implementing RFID authorization provides tangible operational advantages:
- Prevent Unauthorized Use – Only approved personnel access assets
- Enhance Accountability – Every interaction is linked to a user
- Automate Records – Borrowing and returning assets require minimal manual input
- Increase Operational Transparency – Managers can track assets in real time
- Enable Data-Driven Decisions – Usage analytics inform maintenance, allocation, and process improvements
These benefits translate directly into cost savings, efficiency gains, and improved compliance.
Implementation Challenges
Despite clear benefits, RFID authorization systems require careful planning:
- Complex Permission Structures – Balancing security with workflow efficiency is critical
- Data Accuracy During Setup – Every asset must be correctly tagged and registered
- Employee Training – Staff must understand how to interact with RFID systems properly
- Integration with Existing Systems – Connecting RFID data with ERP, CMMS, or HR platforms ensures full operational value
Pilot deployments often help organizations refine permission rules and ensure smooth adoption before scaling up.
Comparing RFID Authorization with Traditional Methods
Aspect Traditional Methods RFID Authorization
Access Control Manual checks, forms Automatic verification via RFID
Usage Records Paper or spreadsheet logs Real-time digital records
Security Dependent on compliance Proactive enforcement with alerts
Operational Visibility Limited Instant insights on asset usage
Accountability Hard to trace Each interaction is linked to a user
The comparison demonstrates why organizations increasingly replace manual processes with automated RFID solutions.
FAQ: RFID Asset Authorization
Q1: What is RFID asset authorization management?
RFID asset authorization management is a system controlling who can access, move, or use specific assets. It combines asset tagging, personnel identification, location awareness, and permission rules.

Q2: How does RFID control asset permissions?
The system links user identities with asset tags and evaluates permission rules in real time, allowing or blocking actions and logging all interactions.
Q3: Which industries benefit from RFID authorization?
Manufacturing, IT, laboratories, healthcare, and any environment with shared or high-value assets benefit from RFID authorization.
Q4: What are common challenges in implementing RFID permission systems?
Key challenges include designing effective permission structures, ensuring data accuracy, training employees, and integrating with existing IT platforms.
Q5: How does RFID improve accountability and security?
Every asset interaction is linked to a user and timestamped, providing transparent records and real-time alerts for unauthorized actions.
Key Takeaways
RFID permission and asset authorization management provides more than tracking. It ensures only the right people access the right assets under controlled conditions, enhancing accountability, transparency, and operational efficiency.
Organizations implementing these systems can expect:
- Automated, accurate borrowing and usage records
- Proactive enforcement of permission policies
- Reduced operational risks and unauthorized asset usage
- Actionable analytics to optimize asset utilization
As enterprises increasingly rely on shared, high-value, or sensitive equipment, RFID-based authorization is no longer optional—it is a core component of modern asset management strategy.